Search results for "crypto"
End-to-End security ensures virtualisation is viable
In applications such as industrial control and telecom the business-level benefits of virtualisation are becoming more understood.Companies worldwide have analysed real-world use cases and concluded that major savings in lifetime operational costs are achievable by deploying software-based, virtualised systems compatible with open standards, instead of traditional fixed-function physical equipment based on proprietary, vertically integrated archi...
Beating hackers with hardware security devices
Earlier this year, cryptocurrencies valued at $530m were stolen in a hack on a Japanese cryptocurrency exchange. Reportedly, slack security practices made the exchange vulnerable because the money was stored in a poorly-secured digital wallet. If the exchange had been using a hardware security device, the hack probably wouldn't have succeeded. Guest blog written byMark Patrick, Mouser Electronics.
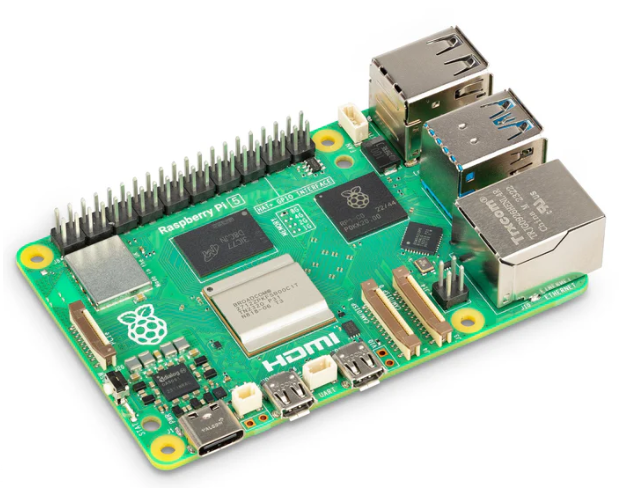
Development board kick starts low-power wireless designs
The Tiger board extends the SmartEverything family at Arrow Electronics. It features the NXP Semiconductors Kinetis KW41Z multi-protocol wireless MCU for extremely low-power connected devices. The board provides an ideal platform for products like smart door locks, portable healthcare technology, wearable sports monitors, RF remote controls, wireless computer keyboards and mice, gaming controllers, security access-control systems, smart energy pr...
Delivering optimal network computing
Lanner has released the NCA-5520, a 1U 19” rackmount network appliance built with IntelXeonProcessor Scalable Family (Codenamed Skylake-SP).The introduction of the NCA-5520 is a response to network service providers’ demand for more agile and flexible methods for delivering network computing performance while saving ownership costs; the NCA-5520, featuring computing power and virtualisation capacity in a compact 1U form factor with hi...
The ST33 - a trusted platform for automotive applications
The ST33GxxxA is a serial access microcontroller designed for secure mobile applications that incorporates the most recent generation of ARM processors for embedded secure systems.
Automatic emergency call saves lives
It can save lives, which is why the automatic emergency call feature – termed eCall – will be mandatory for all new car and light commercial vehicle models in the European Union from 31st March 2018. It will therefore be integrated in future in an estimated 20 million new vehicles annually.The aim of the eCall system is to shorten the time between an accident and the arrival of the emergency services by up to 50% throughout Europe, an...
The thermodynamics of computing
Energy-saving computer systems could make computing more efficient, but the efficiency of these systems can’t be increased indefinitely, as ETH physicists show.As steam engines became increasingly widespread in the 19th century, the question soon arose as to how to optimise them. Thermodynamics, the physical theory that resulted from the study of these machines, proved to be an extremely fruitful approach; it is still a central concept in t...
Mitigating security vulnerabilities like Meltdown and Spectre
Rambus has announced the availability of the CryptoManager Root of Trust, a fully programmable hardware security core built with a custom RISC-V CPU. The secure processing core creates a siloed architecture that isolates and secures the execution of sensitive code, processes and algorithms from the primary processor.
The increasing need for security throughout an IIoT system
At Embedded World, Real-Time Innovations has announced a live demo of Connext DDS Secure to highlight the increasing need for security throughout an IIoT system. The demo features Connext DDS in a Healthcare application, specifically a secured integrated clinical environment (ICE). This security architecture can easily extend to other markets, such as autonomous vehicles, smart grid/energy, and aerospace and defense.
Regulation within crypto currency markets
Japan’s financial regulator has said it has ordered all cyrptocurrency exchanges to submit a report on their system risk management, following the hacking of over half a billion dollars of digital money from Coincheck.Whilst the whole premise of blockchain technology and crypto currencies revolves around it being essentially unhackable, the exchanges that trade these currencies are vulnerable. Written byAlex Larsen, CFIRM, Institute of Ris...