Cyber Security
Cyber Security
Protecting infrastructure from cyber attack
In October 2016, the UK government launched the National Cyber Security Centre (NCSC) aimed at enhancing the country’s ability to deal with cyber threats. The move outlined the growing importance of cybersecurity in both the private and the public sector. Here, Nick Boughton, Digital Lead at Boulting Technology, shares his advice for making critical infrastructure more secure.
Dual-use commercial tech creates significant growth opportunities
Frost & Sullivan’s recent analysis, US DoD Cybersecurity Market, Forecast to 2023, reveals that intense attacks from adversaries and non-state actors are compelling Department of Defense (DoD) cybersecurity spend for commercial off-the-shelf (COTS)-based cybersecurity tools and systems and the development of quantum computing and artificial intelligence technologies. Defense cybersecurity industry consolidation is expected to increase w...
Keeping up with the changing face of security
We have been lucky in 2018 after the terror that tore across Europe and the UK in 2016 - 2017 with vehicle, knife and bomb attacks happening in Nice, London Bridge, Westminster, Manchester and Barcelona. These are just a few of the places left reeling from a wave of extremism targeting people going about their normal lives and enjoying themselves. The often crudeness of the weaponry used belies the sophistication of many of the attacks. By Phili...
Act efficiently to identify malicious actors targeting networks
Provider of the industry's extensible, intelligence-driven security platform, ThreatConnect, has announced its integration with Dragos WorldView intelligence, which delivers critical insight about threat activity groups specifically targeting industry control networks (ICS) worldwide.
Security research reveals password inadequacy still a top threat
New research from the WatchGuard Threat Lab shows the emergence of the Mimikatz credential-stealing malware as a top threat and the growing popularity of brute force login attacks against web applications. The research also reveals that 50% of government and military employee LinkedIn passwords, largely from the US, were weak enough to be cracked in less than two days.
Cyborg cockroach may save your life one day!
A cockroach no bigger than a large paper clip scurries across the floor of Abhishek Dutta’s lab at the University of Connecticut. Some scientists might be shocked to see such a notorious visitor occupying their research space. But not Dutta. He watches intently as the roach moves left, and then right, then left again, as it traverses the cool tile floor. His interest is well-founded, for he is the one initiating the tiny creature&rsquo...
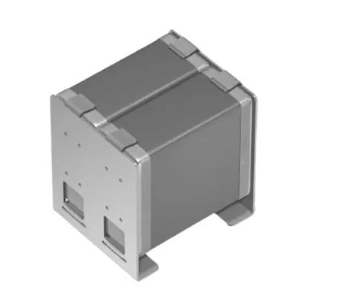
Hardware-based security solution
A turnkey security solution which provides robust security to the diverse applications in the Internet of Things, ranging from industrial automation systems and smart homes to consumer devices, the OPTIGA Trust X, is available from Rutronik. The high-end security controller comes with full system integration support for easy and cost effective deployment of advanced security measures.
Networks deliver new choices in deep ICS network visibility
Nozomi Networks has announced a new product line designed to support mature and sophisticated ICS cyber security programmes. SCADAguardian Advanced (SGA) provides full asset information by combining passive network monitoring with a safe, active approach for the best overall solution. New Smart Polling capabilities allow users to safely gain precise real time asset inventories for stronger network monitoring.
Taming the tsunami of bots, apps and cloud infrastructures
SailPoint Technologies Holdings continues to drive innovation with IdentityIQ to help organisations embrace thenew frontiers in identity governance, which address the explosion of new users, applications and data driven by digital transformation. With IdentityIQ 7.3, SailPoint expands the definition of identities beyond humans, providing the ability to govern non-human identities such as software bots, including robotic process automation (R...
Hackers holding customer data to ransom
News has broken that Superdrug has become the latest high street chain to be targeted by hackers holding customer data to ransom. According to the store, hackers contacted them on Monday evening saying they had obtained details on approximately 20,000 customers.