Cyber Security
Cyber Security
Three levels of security to protect passwords
A new approach to password security has launched, with three levels of security to keep passwords private. Mycena Password Fortress is a patent-pending free to download mobile app which acts as a fortress with three levels of security within the user’s device. The app doesn’t use a master password and heralds in reinforced security with a combination of identification protocols.
A better security system means a secure building
Last year, ONS figures reported the number of burglary offences hit over 420,000, which is a major concern for businesses, facilities managers and homeowners alike. That’s almost 50 burglaries every hour! Having an efficient alarm system that’s reliable is essential to protect against break-ins. Today, complete alarm system kits are not only affordable but also suitable for any building, no matter the size or location. There are sever...
End-to-end LoRa security solution provides secure key provisioning
As the LoRa (Long Range) technology ecosystem accelerates, security remains an area for improvement in the market due to vulnerabilities that leave the network and application server keys accessible in the memory of modules and microcontrollers (MCUs) paired with a LoRaWAN stack. If keys are accessed in a LoRaWAN device, a hacker can impersonate it and authorise fraudulent transactions, which can result in a scalable attack with substantial ...
Filling the identity-shaped holes in business security
IT leaders are under tremendous pressure today - and it is only getting worse. Not only are they charged with enabling users to be productive, but they must also act as the virtual gatekeepers of enterprise security. These teams address rising threats and compliance challenges amid the digital transformation, which nearly every organisation is undergoing. It can be overwhelming. By Juliette Rizkallah, Chief Marketing Officer, SailPoint
Single-chip security solutions offer simple implementation
Designers of Internet of Things (IoT) devices can now access the highly integrated MAX36010 and MAX36011 single-chip security supervisors from Maxim Integrated Products. These security solutions make it easier for designers to implement robust tamper detection, cryptography and secure storage while safeguarding sensitive information via logical and physical protections, without having to be security experts themselves.
$8.4m awarded for autonomous cyber hardening technology
Developer of commercial embedded software assurance tools and cyber security solutions, GrammaTech, announced that it has been awarded an $8.4m four year contract from Defense Advanced Research Projects Agency (DARPA), to develop technology that generates and deploys secure configurations to commercial off-the-shelf (COTS) equipment rapidly and largely autonomously.
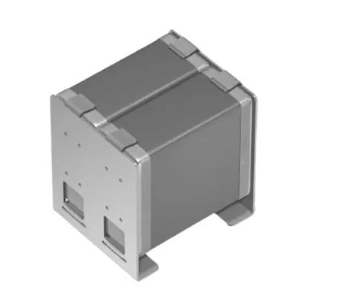
Enhanced data security achieved via integrated hardware
The new C877 from Aitech provides one of the most powerful combinations of data processing and cyber security available in a 3U VPX single board computer (SBC). Based on independent research and data analysis, it was specifically designed for rugged, high reliability, mission-critical environments that need high levels of data security and peak processing performance.
UNECE to integrate ISA standards into cyber security
The United Nations Economic Commission for Europe (UNECE) has confirmed it will integrate the widely used ISA/IEC 62443 series of standards into its forthcoming Common Regulatory Framework on Cyber security (CRF). The CRF will serve as an official UN policy position statement for Europe.
Next generation industrial cyber security platform
Today the IIoT infrastructure has encountered increasing cyber security threats due to the vulnerability by the use of public networks for IT/OT convergence. This has exposed exploitable opportunities for hackers. To add confidence in industrial control system (ICS), Lanner presents LEC-6041, the next-generation industrial cyber security gateway.
Cyber criminals target iPhone users with phishing scams
A new cell phone scam targeted at iPhone users tries to steal their Apple login details by sending a fake Spotify/iTunes email. The phishing email claims to be from Apple and Spotify. If a user clicks on the link, the email says the user had bought a year of Spotify Premium for $150.99 and links to a page to ‘review your subscription’. A fake Apple landing page – which looks like a real one - then asks for log-in details.